Anbert Endres, Dieter Rombach: A Handbook Of Software And Systems Engineering
Table of Contents
Information Hiding/Encapsulation (IH/E)
Variants and Alternative Names
- Parnas' Law1)
Context
Principle Statement
Modules should be encapsulated.
Description
Information hiding and encapsulation are sometimes seen as one and sometimes as two separate but related notions2). This varies through literature. There are three stages of information hiding/encapsulation which can be defined as having a capsule, making the capsule opaque, and making the capsule impenetrable.
Having a capsule means that an object has methods which enable the client of the module to use it without accessing its internal data structures. Making the capsule opaque means that the inner workings are hidden from the clients. This is typically done by using access modifiers (private, protected). Lastly making the capsule impenetrable means that no client should be able to get a direct reference to an internal data structure.
A properly encapsulated module with an impenetrable capsule is better than an module with just an opaque capsule. And this is better than a module with a non-opaque capsule. But at least having a capsule is better than not having one at all.
Rationale
When the inner workings of a module are hidden from the outside, then they can be changed without any other module noticing it. If the interface of the module stays the same, the rest of the system is not affected by the change. So adhering to IH/E prevents ripple effects.
Strategies
- Use the lowest possible visibility for a variable or method
- Make all attributes private and use getter and setter methods to access them
- Better also avoid getters and setters
- Find suitable abstractions for data types and use appropriate methods instead of just getters and setters
- Avoid aliasing problems with value objects
- If the programming language supports that use call-by-value objects (like stack objects in C++, structs in C#, records in Delphi, etc.) for value objects like
Date,Money,EMailAddress,TelephoneNumber, etc. - Otherwise use immutable objects which are handled call-by-reference but needn't be copied
- Avoid aliasing problems with lists and similar data structures
- Copy internal list objects before returning them or only return a read-only
interfaceto them
Caveats
See section contrary principles.
Origin
David L. Parnas: On The Criteria To Be Used In Decomposing Systems Into Modules
Evidence
Relations to Other Principles
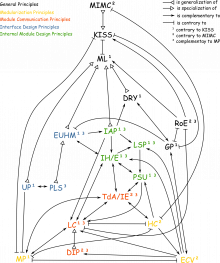
Generalizations
Specializations
Contrary Principles
- Keep It Simple Stupid (KISS): Not adhering to IH/E is often easier.
Complementary Principles
- Model Principle (MP): IH/E demands having an interface for a module which hides the inner workings. MP tells how such an interface can look like.
- Liskov Substitution Principle (LSP): For subclasses you can waken encapsulation by having a wider
protectedinterface which can be used by subclasses. For these cases LSP has to be considered, too. - Tell, don't Ask/Information Expert (TdA/IE): Encapsulation is about not having getter methods returning constituent internal parts of a module. TdA can be another reason for that.
- Low Coupling (LC): Higher forms of couplings (especially content couplings) break encapsulation.
- Principle of Separate Understandability (PSU): IH/E is about constructing a module in a way that hides the inner workings so it can be used without knowing them. PSU on the other hand is about constructing a module such that its inner workings (and its usage also) can be understood without knowledge about other modules.
- Easy to Use and Hard to Misuse (EUHM): A module should be properly encapsulated in order to make it easy to use and hard to misuse.
Principle Collections
Examples
Example 1: Date and Time
In Delphi there is the data structure TDateTime which represents a specific date and time value 4). This is an alias name for a double value where the integer part represents the number of days since December 30, 1899 and the fractional part represents the time of day. This alone is a data structure but it is not encapsulated.
The Delphi runtime library (RTL) now specifies functions which operate on TDateTime structures. This is “having a capsule”. But since it is still possible to access the internal representation directly, the inner workings are not hidden.
This is different in Java. Here the inner workings are hidden. It is not possible to access the private attributes of java.util.Date5). Here the capsule is opaque (and impenetrable).
Example 2: Aliasing
A typical example for an opaque but penetrable capsule is the following:
class SomeClass { private SomethingDifferent innerObject; public SomethingDifferent getInnerObject() { return innerObject; } }
In such a case the innerObject is private, which means it is hidden. But it is revealed by the getter method. In order to establish an impenetrable capsule, the object has to be copied:
class SomeClass { private SomethingDifferent innerObject; public SomethingDifferent getInnerObject() { return innerObject.clone(); } }
Description Status
Further Reading
Discussion
Discuss this wiki article and the principle on the corresponding talk page.